So from the previous log... I dumped the entire G5 binary inside. Looks fun? Nope. Full of corrupted binary, I jiggled these wires again and again just to get something consistent. And, it doesn't start when I launched it in the EmuVT.
The lucky part is, there's no data bits being swapped. All the sprites and tiles are in an original condition.
The more difficult part is: this thing has bits swapped in its opcodes at its startup! I managed to track them when I see familiar numbers such as $412D and $4137 and with a lot of other strange opcodes that don't make any sense.
Playing around with the bits (and with some previous knowledge on the other 400-in-1 handhelds) I noticed that bits 6,7 and bits 1,2 are swapped on its opcodes. The operands are spared in this process.
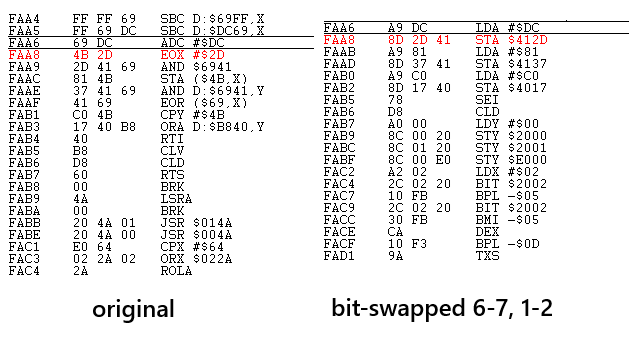
Compared to the other handhelds, the bit-swaps are not just the first few instructions - it has about 200 bytes of them! I wrote a Python script, managed to undo all the bit swapping and it runs now on the emulator!

I am not entirely sure if this first 512KiB of that program will work anymore when it is placed back into the original handheld (of course with the bits being untouched). A broken dump would mess up the TFT initialization routines inside and could render this whole thing useless immediately! So, at all costs, that startup code must be preserved!!
 YH-workshop
YH-workshop
Discussions
Become a Hackaday.io Member
Create an account to leave a comment. Already have an account? Log In.